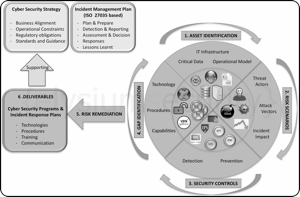
Having a plan, or not, to secure your enterprise and respond to an incident could be the difference between closing down your company or seeing that incident through!
Most large organisations invest considerable amount of time, money and resources to define a Cyber Security Strategy resulting in several Cyber Security Programs and Incident Management/Response Plans.
All of which are in support of a wider Business Continuity Plan (BCP).
This results in procedures, documentation, backup systems, regular incident simulations and dedicated teams.
As long as these initiatives are kept up to date and still relevant to the organisation mode of operation then it should help a company survive most incidents.
By contrast, smaller organisations and especially start-ups tend to focus first on getting the "job done" and then think of what to do in case of an emergency or incident.
Their Cyber Security Programs and Incidence Response Plans are often limited to t...
>>[READ MORE]
{elysiumsecurity} 
Cyber Protection & Response
Security News (127 Posts)
 Cyber Security Planning - A simple 6 Steps Approach
Cyber Security Planning - A simple 6 Steps Approach
 The 2015 SANS Holiday Hack Challenge Write-Up
The 2015 SANS Holiday Hack Challenge Write-Up
For the last 12 years, SANS/Counterhack offers a hacking challenge over the Christmas period. It is a great event, fun and with an increasing level of difficulty which lets everyone having a go.
This year, The 2015 SANS Holiday Hack Challenge was built around a great 8-bit retro web gaming platform where you had to run around a virtual town to find the various hacking challenges.
The plot was centered around a fictitious toy, a gnome, that everyone wanted to have in their home for Christmas. However, two kids found the toy was "behaving" strangely and something was going on.
Through the challenge you will learn that the gnomes had in fact a hidden built-in camera and were transmitting photos to 5 super gnomes (servers) by connecting to free surrounding WIFI netwo...
>>[READ MORE]
 How to build an efficient Anti-Phishing Framework?
How to build an efficient Anti-Phishing Framework?
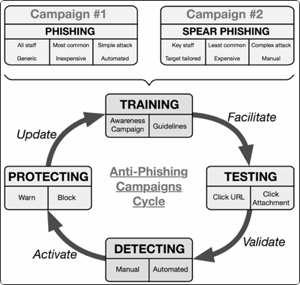
As our world reliance on electronic connection and communication is accelerating, cyber attacks are on the rise along with
counter measure solutions in the form of endless new cyber security companies, consultants, expertise, software and hardware
aimed at protecting individuals, assets, corporations and even nation states.
However, even with all the tools and increasing cyber budget at our disposal, there is always one constant weak link:
The Human element in the so called Cyber Kill Chain.
It is this human element that can defeat the most sophisticated defence systems and it is why the use of Phishing and
Spear Phishing attacks are so prominent and successful.
Those attacks exploit human emotion, ignorance and credibility to bypass defences in tricking users to follow poisonous steps:
Clicking on links, opening documents, accepting/ignoring security warnings and good practises, installing software, etc....
>>[READ MORE]
 How to build a Red Team and Why?
How to build a Red Team and Why?
I recently gave a talk at the Rant Forum in London on the topic of
"RedTeam, why this is more than a buzz word?".
It was an interesting experience and whilst different from traditional security events, as the crowd can and will interrupt you at any time, it was very enjoyable.
Many attendees asked if I could produce some "slides" after the talk. As no slides were used, below is a collection of notes from wich the talk was based on.
In this post we will explain what RedTeam is, how does it fit with other similar security services and what advantages does it bring to an organisation.
We will also look into what works? what doesn’t? And where is this “new” type of service going?
1. DEFINITION
A Red Team is part of a trio of services which increases in sophistication: Vulnerability Assessment, Penetration Testing and then Red Teaming.
We will d...
>>[READ MORE]
 RANT FORUM - Red Team Recipes Presentation
RANT FORUM - Red Team Recipes Presentation
I will be giving a talk tomorrow evening, the 28th of November at around 6pm, in London at the Risk and Network Threat (RANT) Forum .
The topic is:
Why RedTeam is more than just a buzz word? What works? What doesn't? And where is this "new" type of service might be going? All those questions answered by someone who is actually delivering Red Team activities.
Registration is free, you get free drinks and food... plus you get to hear me talk, so what is not to like?! :)
You can register HERE
The RANT Forum is quite different from your typical free security briefing, for a start it is not a sales forum. However, the company behind it is a recruitment agency, so they are still interested in taping the UK Security professional community!
...
>>[READ MORE]
 IDS used as a Network Forensic Tool
IDS used as a Network Forensic Tool
Note: This is the second post of a two parts series on how to use IDS in a different way.
Intrusion Detection Systems are traditionally seen as Defensive tools. They can however be used for different purposes than initially designed for as highlighted in the previous post , where we discussed how IDS could be used as an offensive tool.
The popularity of pre-configured/packaged IDS environments such as SELKS or Security Onion provide various software packages and Graphical User Interfaces to navigate through large volume of data by parsing/categorising/filtering it automatically.
More importantly, such systems are starting to provide mo...
>>[READ MORE]
 IDS used as an Offensive Security Tool
IDS used as an Offensive Security Tool
Note: This is the first post of a two parts series on how to use IDS in a different way.
Intrusion Detection Systems such as Snort and Suricata
are traditionally seen as Defensive tools, and in essence they are. They can alert on security issues occurring on your network such as Botnet Activities, network based attacks, hosts/servers activities and vulnerabilities.
That last point is important.
It is important because that same information used for defence activities, could be used by an attacker as part of an attack reconnaissance. For example, being able to identify a list of hosts that use outdated SSH/SSL servers, a vulnerable Flash Client or other vulnerable software/services; HTTP logs highlighting users web activities, clear text passwords, etc.
When looking at an IDS that way, it becomes a passi...
>>[READ MORE]
 Securing your Cloud Storage with a Boxcryptor alternative called EncFS
Securing your Cloud Storage with a Boxcryptor alternative called EncFS
Cloud storage providers such as Dropbox, Box, One Drive, etc. are increasingly being used for both personal and business reasons. On the Business side, often without the individual's company fully aware of what data is actually leaving their premises.
One of the issue with storing data in the cloud is Security. Looking at Dropbox in recent years, there has been a number of embarrassing blunders which resulted in their customers' data becoming available to anyone who knew where to look. We did blog about it several times: here, here and here. Many other security blogs also related those stories, such as this nice summary from Sophos.
To limit the risks relat...
>>[READ MORE]
 How to reduce WEB 2.0 attack surface by going back to WEB 1.0, the dynamic way!
How to reduce WEB 2.0 attack surface by going back to WEB 1.0, the dynamic way!
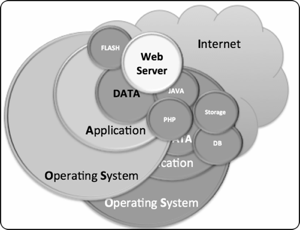
The arrival of WEB 2.0 brought dynamic content through the use of technologies such as Java, Flash and PHP.
Consequently it also widen the attack surface. Websites became prettier, more interactive, easier to update and also easier to attack!
The need for further functionality was, as it is often the case, at the cost of security.
The four diagrams below illustrates the differences between a WEB 1.0 and a WEB 2.0 architecture as well as highlighting the increased attack surface.
In a typical WEB 1.0 architecture, besides the physical, human and network security considerations, protecting the data is dependant of the Operating System and the application security layers. Typically, the application security layer is restricted to the Web Server (i.e.: Apache) if no other services/applications are exposed to the Internet.
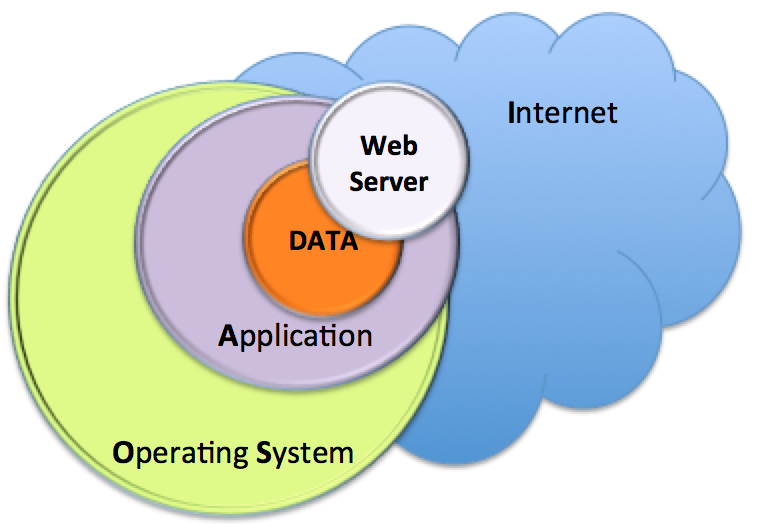
Diagram 1 - WEB 1.0 Typical Ar...
>>[READ MORE]
 SELKS 2.0 vs. Security Onion
SELKS 2.0 vs. Security Onion
I have recently been testing SELKS v2.0 which is an open source Network Security Monitor (NSM) based on an
ELK framework: Elasticsearch (search and analytics engine) Logstash (log normalisation) Kibana (visualisation).
The NSM core engine is provided by the first "S" which stands for Suricata (Network IDS) and the last "S" which stands for Scirius (Management GUI for Suricata).
SELKS is provided as a live Linux distribution based on Debian 8 (Jessie) which is also installable.
SELKS V2.0 is a great improvement from SELKS V1.0, so much so that I now consider it a serious contender to Security Onion (SO) at...
>>[READ MORE]